User Logins and Management
Canonic has a uniquie type of user table that lets you manage & store your users data along with the capabilities of suppporting different login providers. We support GITHUB, GOOGLE & FACEBOOK as of now.
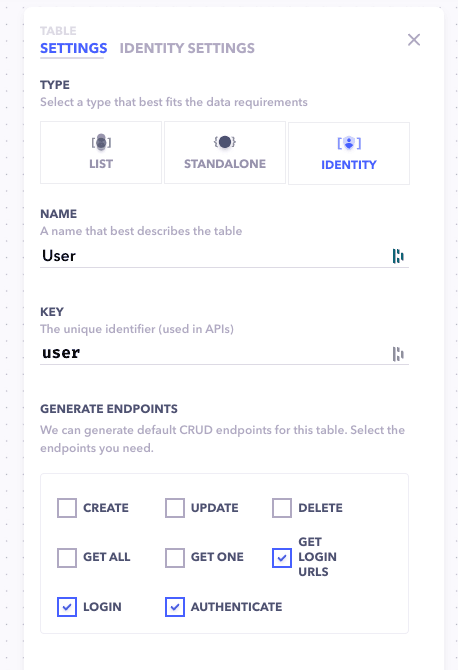
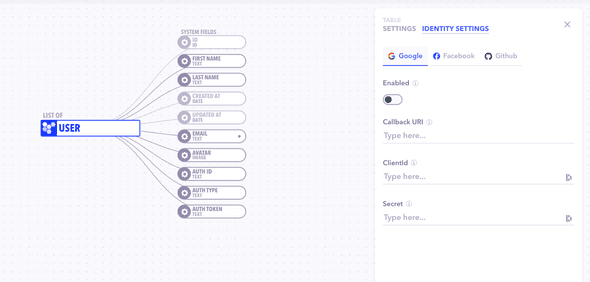
When you create an identity type table in your new or existing project, it'll come with a bunch of predefined system fields that covers most of the user information. You can also add more fields to this table as you require.
You can choose and enable which login provider you want your backend to support and fill in the required details for them.
- Client ID → The Client ID of the project issued from login provider.
- Secret → The Secret key of the project issued from login provider.
- Callback URI → The URL of the application where you want your users will be redirected after logging in.
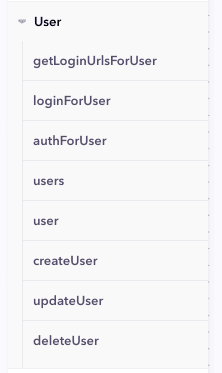
Once you fill in the required paramaters, you are set to go and hit deploy. Canonic will spit out a unified set of API's (along with it's documentation) for login, authentication and managing your users inrespective of from which source they are loging in.
How to handle User Logins
There are two main flows typically that come up for handling user logins:
- Signing up a new User
- Authenticating returning user
I - Signing Up a new User
Step 1: Fetch Redirect URL
After providing the option to Signup or Login through the providers in your frontend, you need to redirect the user to their specific login urls. You can get them by calling the getLoginUrlsForUser API.
| API | Method | Description |
|---|---|---|
| getLoginUrlsForUser | GET |
Returns the URLs to which the user must be redirected to login, for all the providers enabled in the identity settings table. |
Example Query:
query Login {
getLoginUrlsForUser {
GOOGLE
GITHUB
FACEBOOK
}
}Step 2: Logging the User
When the user completes the signup or login, the provider will redirect the your app to the Callback URL (that you added in your identity table settings) along with a token appended to it.
Call the loginForUser API and pass the retreived token from service provider along with the type of the provider. It'll get the users details passed by the provider, store it and send them back to you. It'll also send you an auth token to authenticate the user without making him to login again the next time.
| API | Method | Description |
|---|---|---|
| loginForUser | POST |
Logs the user in your database. The auth code passed from the provider after loging in, along with the provider type being used must be provided. Returns a JWT token for future authentications along with the details of the user. |
Example Mutation:
mutation Login($code: String!, $service: String!) {
loginForUser(code: $code, service: $service) {
token
user {
email
firstName
lastName
avatar {
url
}
}
}
}II - Authenticate returning User
Send the stored auth token to the authForUser API to authenticate the user and let him in. It'll return a valid token which you can replace with your existing one along with the user's details.
| API | Method | Description |
|---|---|---|
| authForUser | POST |
Tries to authenticates a user. The JWT token stored for the user must be provided. Returns the details of the authenticated user and a valid token for next time authentication. |
Example Mutation:
mutation Login($token: String!) {
authForUser(token: $token) {
token
user {
email
firstName
lastName
avatar {
url
}
}
}
}The API can also return an error saying
invalid_tokenortoken expired. In that case, you'll need to redirect the user to the respective providers and log him again. To do that, just repeat the signup flow mentioned above, canonic will take care of the rest.
That's all you need to do to manage user logins and signups. It cuts down all the boiler plate code, sets up different logins in a few easy steps and manages your users data in a secure way.
Canonic also gives you all the CRUD APIs for your user identity table in case you need to build any other flows according to youe product needs.
User Table CRUD APIs
| APIs | Method | Description |
|---|---|---|
| users | GET |
Retrieves all the users. Supports filtering based on keys |
| user | GET |
Retrieves a single user based on the id provided |
| createUser | POST |
Creates a new user in your table. Returns the user object. |
| updateUser | PATCH |
Updates a specific user. Only keys that need to be updated need to be provided along with the id to be updated. Retuns the updated user object. |
| deleteUser | DELETE |
Delete a specific user. The id for the user to be must should be passed. |